Network security is a critical fortress against evolving threats in today’s interconnected digital landscape. Understanding the top 10 common network security threats is paramount in safeguarding sensitive data and infrastructure. From malicious software to sophisticated cyber-attacks, this comprehensive exploration aims to shed light on prevalent threats jeopardizing networks worldwide.
Malware
Malware, short for malicious software, encompasses a diverse array of digital threats designed to infiltrate, damage, or gain unauthorized access to systems. Viruses, ransomware, and worms represent a trifecta of destructive intent within this category. These insidious programs leverage various entry points, from email attachments to compromised websites, posing severe network integrity and data confidentiality risks.
Phishing Attacks
Phishing, a prevalent cybercrime tactic, involves deceitful attempts to trick individuals into revealing sensitive information or executing malicious actions. Crafted to mimic trusted entities through emails, messages, or websites, these attacks prey on human vulnerability. Whether it’s through generic mass emails or highly personalized messages, phishing poses a persistent threat, jeopardizing both personal and organizational security.
DDoS Attacks
A Distributed Denial of Service (DDoS) assault floods networks or servers with an overwhelming volume of traffic, rendering them inaccessible to legitimate users. Attackers orchestrate this deluge by exploiting multiple devices or botnets, disrupting services, and causing downtime. DDoS strikes vary in scale and sophistication, posing a significant challenge for network resilience and necessitating robust mitigation strategies.
Man-in-the-Middle (MitM) Attacks
Man-in-the-Middle (MitM) attacks intercept and manipulate communication between two parties, often without their knowledge. Operating secretly, hackers position themselves between the sender and recipient, eavesdropping on or altering transmitted data. By exploiting vulnerabilities in unsecured networks, these attacks compromise sensitive information, emphasizing the criticality of encryption and secure communication protocols to thwart such intrusive breaches.
Insider Threats
Insider threats stem from individuals within an organization exploiting access privileges or inadvertently causing security breaches. Employees, contractors, or partners can compromise data integrity through malicious intent or unwitting actions. Implementing robust access controls and fostering a culture of security awareness are vital defenses against these internal risks.
Password Attacks
Password attacks encompass various techniques like brute force and dictionary attacks, aiming to crack user credentials. Weak or reused passwords pose vulnerabilities, making systems susceptible to unauthorized access. Employing multifactor authentication, enforcing strong password policies, and regular password updates are vital in fortifying defenses against such assaults.
SQL Injection
SQL Injection exploits security vulnerabilities in web applications, permitting attackers to manipulate databases using malicious SQL code. By injecting rogue commands into input fields, hackers gain unauthorized access to sensitive data or execute unauthorized operations. Robust input validation and parameterized queries are essential defenses against this prevalent attack vector.
Zero-Day Exploits
Zero-day exploits target undisclosed vulnerabilities, exploiting security flaws before developers can provide patches. These attacks exploit the unknown, leaving systems vulnerable to infiltration or manipulation. Timely security updates, threat intelligence monitoring, and proactive security measures are crucial in mitigating the risks posed by these unforeseen threats.
Social Engineering Attacks
Social engineering leverages psychological manipulation to deceive individuals or employees into divulging confidential information or performing actions beneficial to attackers. Techniques include pretexting and baiting, exploiting human trust or curiosity. Combating these attacks involves robust training, skepticism towards unsolicited communications, and a security-aware organizational culture to mitigate these deceptive tactics.
IoT Vulnerabilities
IoT devices, while enhancing convenience, harbor vulnerabilities susceptible to exploitation. Insecure configurations, lack of updates, and weak authentication mechanisms expose these devices to cyber threats. Compromised IoT gadgets pose risks, becoming entry points for network breaches. Implementing rigorous security measures, including regular updates, strong authentication, and network segmentation, is crucial in safeguarding against IoT-related vulnerabilities.
Conclusion
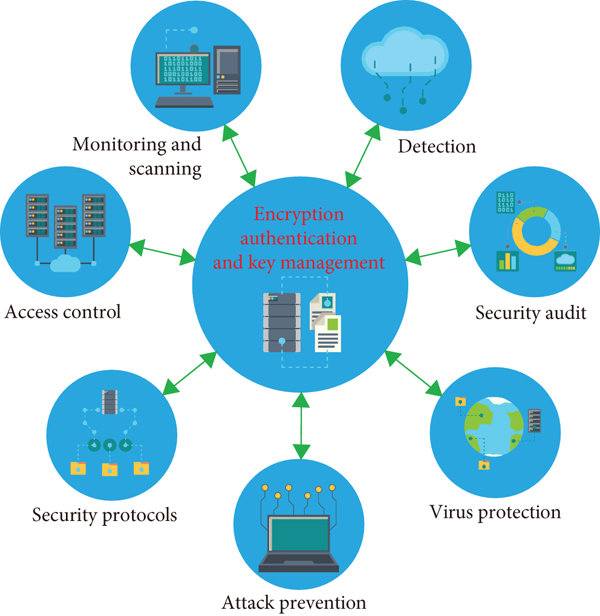
Understanding these top 10 common network security threats is pivotal in fortifying defenses against evolving cyber risks. Services provided by Enterprise Systems, specializing in network security, offer vital solutions to detect and monitor unauthorized access and risks. Through vigilance, proactive measures, and the support of such specialized systems, organizations can fortify defenses and navigate the complexities of cybersecurity effectively.
Read more:


Recent Comments