Stolen passwords offer the fastest path into your network
Insecure password practices are exploited in 81% of cyber attacks worldwide, and 61% of all attacks target businesses with less than 1,000 employees.1 While employee education and training can help, what’s most needed to reverse this trend is for authentication to require additional proof of identity beyond simple username and password, and to be widely deployed by all companies – no matter their size. Only then, will cyber criminals no longer be able to use stolen credentials to access and infect systems or steal data.
Are employees undermining company security with shared passwords?
Most employees are not intentionally trying to compromise company security; however you should ask yourself what password practices they now use to cope with the proliferation of online accounts requiring them. According to an often-quoted study by Microsoft Research, “The average user has 6.5 passwords, each of which is shared across 3.9 different sites. Each user has about 25 accounts that require passwords, and types an average of 8 passwords per day.”
A 2015 Dashlane survey revealed that each person had over 90 online accounts, and had to reset their password using a “forgot password” link for 37 of those accounts in the prior year. Companies that require frequent resetting of passwords make it even harder for users to craft strong passwords and then later recall them. In this environment, it’s understandable that users have simplified their passwords – creating ones that can be serialized – and limiting them to a few that are used across multiple accounts.
1 Verizon’s 2017 Data Breach Investigations Report
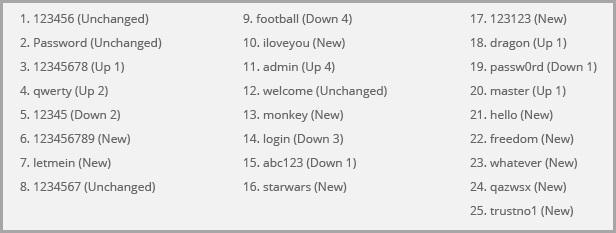
This trend is evident when viewing the list
of worst passwords used:
For businesses, as employees use simpler and weaker passwords – this puts networked resources at a greater risk for breach. Even worse, when an employee’s credentials are stolen from other sites and the credentials happen to contain the same password that gives them entry to your privileged networks, then the hackers can walk right in the front door masquerading as the user…and you are none the wiser.
We’ve reached the limit of the protection that solely password-based access to systems can provide. What’s needed are additional measures to ensure the identity of the user…which is what multi-factor authentication (MFA) provides.
How are hackers stealing credentials?
Given that usernames and passwords are often the only hurdle to accessing systems that yield financial rewards, hackers have taken a keen interest in lifting them when they can. Some common ways to compromise this information include:
- Phishing/Spear-Phishing: Criminals use email to try to get users to enter credentials into web pages or forms. It will look convincingly like an email from a person or business that the user has a relationship with, and sometimes will be very targeted at a specific individual (spear-fishing) who is perceived to have a great deal of privileged system access.
- Brute Force: With simpler passwords coming back into use, criminals will try common passwords until they find one that works. They’ve even written automated scripts that circumvent simple protections such as a limit on the number of authentication attempts within a certain time window. Remember, for businesses without MFA, they just need any single username/password combination to work.
- Wi-Fi Evil Twin: Using an easy-to-find $99 device, criminals can sit in a crowded area and pretend to be a legitimate Wi-Fi hotspot. When people connect, then the criminal is effectively a MitM (man-in-the-middle), observing network traffic and even the keystrokes of a user while connected. Studies have shown that people regularly check bank accounts, shop online, and yes, even access company networks, while on public Wi-Fi.
Once they have valid credentials, they will use them to access systems and steal data, consume resources with botnets, install ransomware, and even steal more credentials that might unlock other networks and personal data.




Recent Comments